To build a two-layer backup plan, start by creating multiple copies of your wallets, seed phrases, and documents, storing them in different secure locations like safes or safety deposit boxes. Use strong encryption and physical security measures to protect each backup. Regularly verify and update your backups to keep them current and reliable. By maintaining layered safeguards, you guarantee your assets stay safe even if one layer is compromised. Learn more about implementing these essential steps.
Key Takeaways
- Develop multiple protection layers using both digital encryption and physical security measures for wallets, seed phrases, and documents.
- Store backup copies in geographically separate, secure locations like safes or safety deposit boxes.
- Regularly update and verify backups, testing recovery processes to ensure data integrity and accessibility.
- Limit access controls and use multi-factor authentication to safeguard digital backups from unauthorized access.
- Reassess and enhance your backup strategy periodically in response to evolving security threats and asset changes.
Acer Nitro V Gaming Laptop | Intel Core i7-13620H Processor | NVIDIA GeForce RTX 4050 Laptop GPU | 15.6" FHD IPS 165Hz Display | 16GB DDR5 | 1TB Gen 4 SSD | Wi-Fi 6 | Backlit KB | ANV15-52-76NK
Beyond Performance: The Intel Core i7-13620H processor goes beyond performance to let your PC do even more at...
As an affiliate, we earn on qualifying purchases.
What Is a Two-Layer Backup Plan and Why Is It Important?
A two-layer backup plan is a strategic approach to securing your critical digital assets, like wallets, seed phrases, and important documents. It involves creating multiple levels of protection, guaranteeing that even if one layer is compromised, your assets remain safe. This approach relies on sound recovery strategies and thorough risk assessment. By evaluating potential threats and vulnerabilities, you can determine where to place backups and how to protect them. Implementing a two-layer backup plan helps you stay ahead of unforeseen events, giving you peace of mind knowing your assets are protected through deliberate, layered security measures. Additionally, understanding contrast ratio and its impact on visuals can help you appreciate the importance of clear, distinguishable layers in your security setup. Recognizing the significance of co-parenting strategies can also aid in maintaining stability and security during transitional periods. Incorporating digital asset management principles can further enhance your overall security strategy, ensuring that backups are organized and accessible when needed. To effectively design your backup layers, considering landscaping principles such as creating natural, resilient barriers can inspire more robust physical and digital security measures.

KAIGERR Gaming Laptop, Laptops with AMD Ryzen 4300U(Up to 3.7GHz), 16GB DDR4 512GB SSD Laptop Computer, 16.0inch Windοws 11 Laptop, 1920P FHD Display, WiFi 6, USB3.2, Type_C
【EFFICIENT PERFORMANCE】KAIGERR Laptop featuring the latest AMD Ryzen 4300U Processor (4 cores/4 threads, up to 3.7GHz). Outperforming the...
As an affiliate, we earn on qualifying purchases.
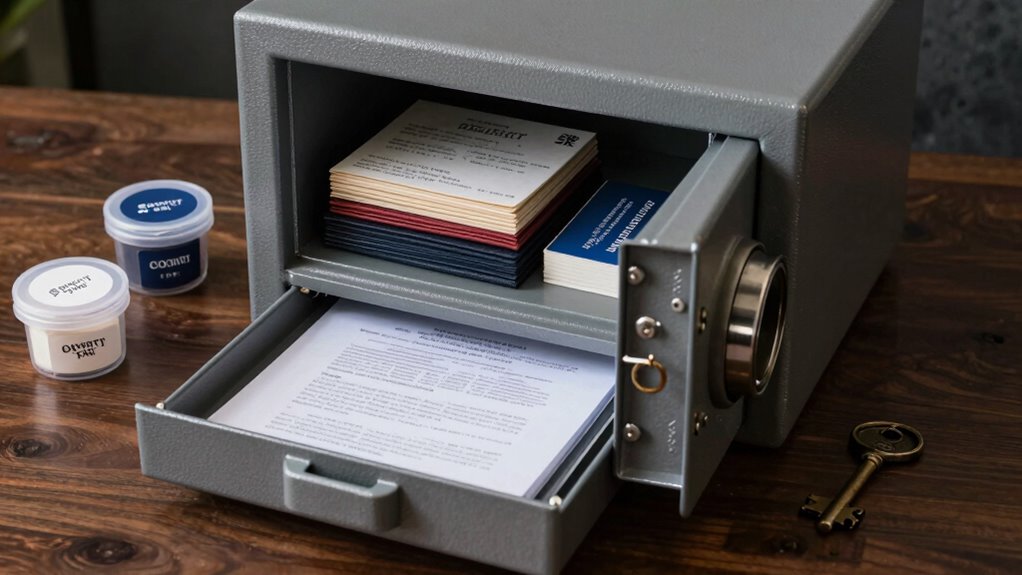
How to Choose Secure Storage for Your Wallets and Seed Phrases
Choosing the right storage methods for your wallets and seed phrases is essential to maintaining their security. You should prioritize encryption methods that protect your data from unauthorized access. Consider using hardware wallets or secure offline devices, as they offer better protection than internet-connected options. When selecting storage locations, avoid obvious places like your home or easily accessible areas. Instead, opt for secure, discreet locations such as safety deposit boxes or physical safes. Make certain these locations are resilient against theft, fire, and water damage. Combining strong encryption methods with carefully chosen storage locations minimizes risks. Regularly review and update your storage choices to stay ahead of potential threats. Additionally, understanding regional cultural significance can help you choose storage options that are both secure and discreet, ensuring your private keys are safe from both digital and physical threats.

ASUS ROG Strix G16 (2025) Gaming Laptop, 16” FHD+ 16:10 165Hz/3ms Display, NVIDIA® GeForce RTX™ 5060 Laptop GPU, Intel® Core™ i7 Processor 14650HX, 16GB DDR5, 1TB Gen 4 SSD, Wi-Fi 7, Windows 11 Home
HIGH-LEVEL PERFORMANCE – Unleash power with Windows 11 Home, an Intel Core i7 Processor 14650HX, and an NVIDIA...
As an affiliate, we earn on qualifying purchases.
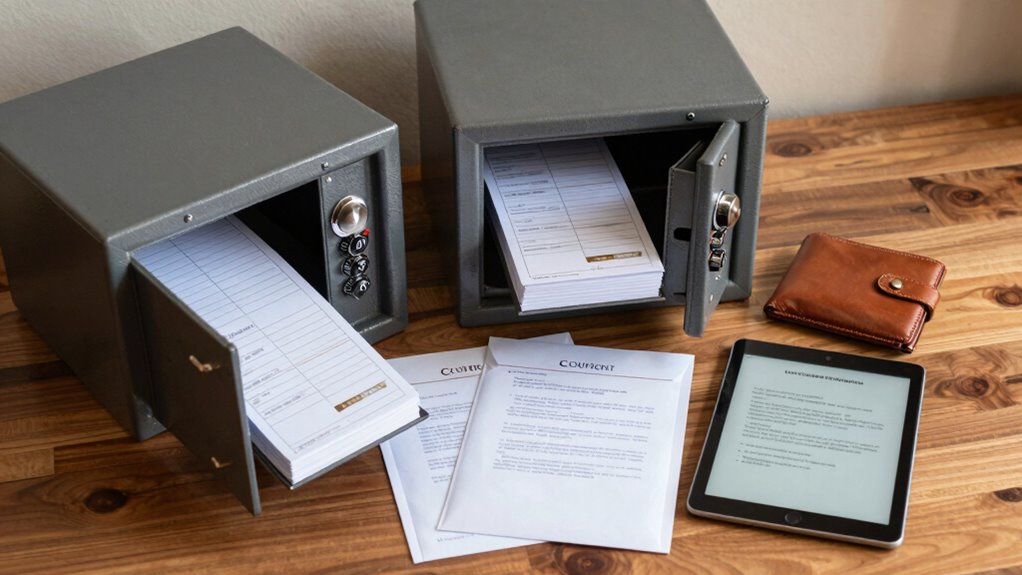
How to Make Multiple Backup Copies for Better Protection

To protect your assets effectively, you should create multiple backup copies and distribute them across different locations. Use secure storage methods like encrypted drives or safe deposit boxes to keep each copy safe. This way, even if one backup is compromised, your other copies remain secure.
Distribute Backups Widely
Distributing backups widely is essential because relying on a single copy leaves your assets vulnerable to theft, damage, or loss. Using distributed storage guarantees your backups are stored in different physical locations, minimizing risk. Employ redundancy strategies by creating multiple copies and placing them in secure, separate places—like a safe deposit box, a trusted friend’s home, or an offsite storage facility. This way, even if one backup is compromised, others remain accessible. Spread out your backups to reduce the chance of complete loss from a natural disaster, theft, or technical failure. Remember, the goal is to ensure your assets are protected through diversity in storage locations, making your backup plan more resilient and reliable.
Use Secure Storage Methods
Securing your backup copies is vital to protect them from theft, damage, or unauthorized access. To do this effectively, use secure storage methods such as:
- Apply strong encryption techniques to digital backups, ensuring only you can decrypt and access the information.
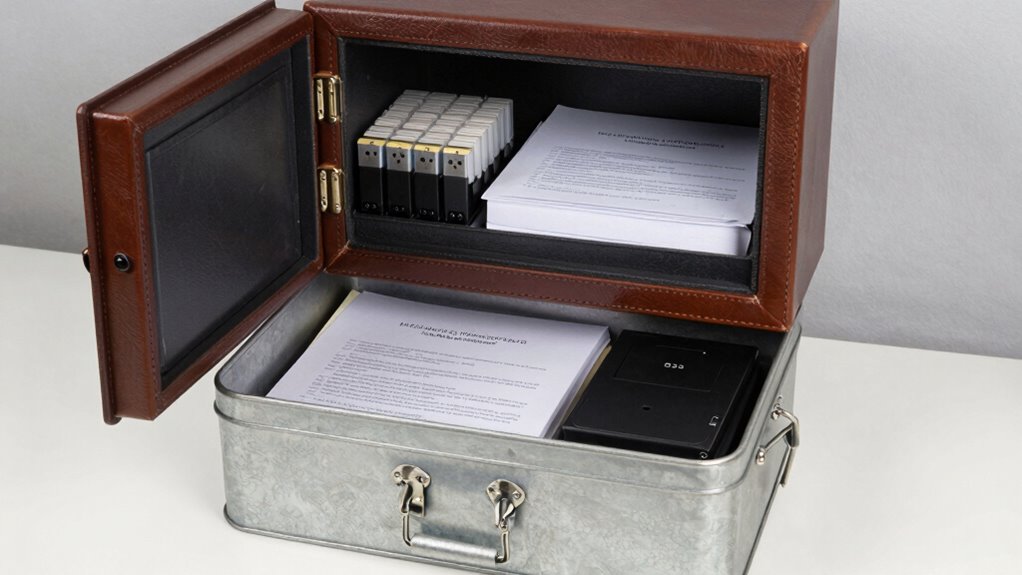
- Store physical copies in high-quality safes or lockboxes, preferably fireproof and waterproof, to prevent damage.
- Keep multiple copies in different secure locations, reducing the risk of total loss from a single incident.
These strategies help safeguard your backups against various threats. Combining encryption techniques with physical safes ensures your sensitive data remains protected, even if one backup is compromised. Proper storage is essential for maintaining the integrity and confidentiality of your backups.
acer Nitro V Gaming Laptop | Intel Core i5-13420H Processor | NVIDIA GeForce RTX 4050 Laptop GPU | 15.6" FHD IPS 165Hz Display | 8GB DDR5 | 512GB Gen 4 SSD | Wi-Fi 6 | Backlit KB | ANV15-52-586Z
Beyond Performance: The Intel Core i5-13420H processor goes beyond performance to let your PC do even more at...
As an affiliate, we earn on qualifying purchases.
How to Secure Your Backup Copies Effectively
Ever wondered how to make sure your backup copies stay safe from theft, damage, or loss? You need to implement strong security measures. Use encryption techniques to protect your data, making it unreadable without a key. Combine this with access controls, restricting who can view or modify your backups. Physical security is vital too—store backups in secure, hidden locations. Consider the following strategies:
| Security Method | Description | Best Practice |
|---|---|---|
| Encryption Techniques | Encrypt data at rest and in transit | Use strong, industry-standard algorithms |
| Access Controls | Limit access to authorized individuals | Implement multi-factor authentication |
| Physical Security | Store backups securely offline or in safes | Use biometric or combination locks |
| Regular Audits | Review security measures periodically | Guarantee controls are effective |
Additionally, understanding data protection laws can help ensure your backup strategies remain compliant and robust. Recognizing the importance of cybersecurity protocols can further enhance your data safety measures. It’s also beneficial to be aware of security best practices specific to your industry or environment to adapt your plans accordingly.
How to Test and Keep Your Backup Plan Up to Date

You need to regularly verify that your backups still work and contain accurate information. Whenever you make changes to your wallets, seed phrases, or documents, update your backups accordingly. Staying proactive guarantees your backup plan remains reliable and effective over time. Additionally, reviewing your privacy policy ensures you are aware of how your data and backup information are managed and protected. Considering the resale value of your assets can also help you understand their worth and ensure your backups reflect current valuations.
Regular Backup Verification
How can you guarantee your backup plan remains dependable over time? Regular backup verification is key. First, schedule consistent backups using effective backup scheduling to ensure your data stays current. Second, test your backups by restoring a small sample to verify integrity without risking your entire dataset. Third, review your encryption techniques to confirm your backups remain secure, especially after system updates or changes. By routinely verifying backups, you catch potential issues early and ensure your data is recoverable when needed. Regular checks help identify outdated or corrupted files, so you can update or re-encrypt backups as necessary. Consistent confirmation keeps your two-layer plan reliable, giving you peace of mind that your wallets, seed phrases, and documents are protected over time.
Update After Changes
Whenever you make changes to your wallets, seed phrases, or important documents, it’s crucial to update your backup plan accordingly. Begin by re-evaluating your backups to ensure they reflect the latest information. Use strong encryption techniques to protect sensitive data during updates, preventing unauthorized access. Strengthen access controls by limiting who can modify or view your backups, reducing risk. Regularly test your updated backups by restoring files in a secure environment, confirming they work correctly. Keep a detailed record of changes and updates to your backup plan. This proactive approach ensures your backups stay reliable, secure, and ready to restore whenever needed. Staying vigilant with encryption and access controls keeps your assets safe as your information evolves. Additionally, understanding your privacy policies and how cookies are managed can help you maintain control over your personal data during these processes. Being aware of software compliance standards can further ensure your backup procedures meet necessary security requirements. Remember to review your security protocols regularly to adapt to new threats and vulnerabilities. Incorporating regular audits of your backup system can help identify potential weaknesses early. Also, staying informed about privacy policy updates can prevent unintended data exposure during backup updates.
Simple Tips to Keep Your Backup Plan Safe and Easy to Manage

Keeping your backup plan safe and easy to manage is essential to guarantee your digital assets remain protected without becoming a hassle. To do this, focus on simplicity and security. First, keep your backup locations separate to enhance emergency preparedness and protect against physical damage or theft. Second, use strong encryption to maintain digital privacy, ensuring only you can access sensitive information. Third, regularly review and update your backups to account for any changes in your assets or environment. This process helps you stay aware of your backup status and ensures your plan remains current and reliable. Additionally, label your backups clearly, so you can quickly find what you need without confusion. Incorporating parallel security layers can further bolster your backup integrity. Understanding the importance of backup etiquette can help you maintain a consistent and secure backup routine. Being aware of physical security measures can also help protect your backup locations from theft or damage. By following these tips, you’ll streamline management and assure your backups are both secure and accessible when needed.
Frequently Asked Questions
What Are Common Mistakes to Avoid in Backup Planning?
You should avoid neglecting redundancy strategies, which guarantee backups remain accessible if one fails. Don’t overlook strong encryption methods, as they protect sensitive data from unauthorized access. Also, avoid storing backups in a single location, risking loss from theft or disasters. Keep backup copies updated regularly, and test your recovery process. Failing to do so can compromise your security and data integrity, making your backup plan ineffective during emergencies.
How Often Should I Update My Backup Copies?
You should update your backup copies at least every three to six months, as data can change or be compromised. Research shows that 30% of data loss happens due to outdated backups. For maximum security considerations, regularly updating your backup frequency ensures your wallets, seed phrases, and documents stay protected against evolving threats. Make it a habit to review and refresh your backups to minimize risks and maintain data integrity.
Can Digital Backups Be Compromised More Easily?
Digital backups can be more easily compromised if you don’t use strong encryption protocols, as hackers target vulnerabilities in cloud services. While cloud storage offers convenience, it’s essential to encrypt sensitive data before uploading and choose providers with robust security measures. Regularly updating your encryption and monitoring cloud vulnerabilities help protect your backups from unauthorized access, reducing the risk of digital compromise.
What Emergency Steps Should I Take if My Backups Are Lost?
If your backups are lost, act quickly—over 80% of data recovery cases succeed with proper procedures. Start by following your emergency procedures, which might include locating a secondary backup or contacting your backup service provider. For backup recovery, use any remaining copies or recovery phrases you have. Stay calm, document your steps, and consider professional help if needed. Rapid response guarantees the best chance of restoring your wallets, seed phrases, and documents.
Are There Recommended Tools for Managing Multiple Backups?
You should consider tools that combine password management with secure cloud storage, like LastPass or 1Password, to manage multiple backups efficiently. These tools encrypt your data and offer seamless access across devices. For added security, use dedicated backup apps like Acronis or Backblaze, which automatically back up your wallets, seed phrases, and documents. This way, you keep your backups organized, protected, and easily accessible in emergencies.
Conclusion
A well-structured two-layer backup plan isn’t just smart—it’s essential for safeguarding your digital assets. Think of it as an insurance policy against unexpected loss or theft. Remarkably, some experts say that no backup system is foolproof—yet, the right strategy can dramatically reduce your risk. By staying vigilant and regularly updating your backups, you’re not just protecting your wallets and documents—you’re securing your peace of mind. Stay proactive, and your digital life remains safe and sound.









